SSU detains deserter registering Starlink terminals for ruscists
Cyber units of the Security Service have blocked yet another attempt by the enemy to gain access to Starlink terminals on Ukrainian territory. Following an operation in Kyiv, an enemy agent who illegally registered communication terminals for the occupiers has been detained.
As the investigation revealed, russia’s task was carried out by a mobilised soldier recruited by the enemy, who had deserted his military unit in the Kharkiv region.
After deserting, the fugitive hid in rented apartments in the capital while seeking ‘easy money’ on specialised Telegram channels.
In one of the Telegram chats, he caught the attention of russian intelligence operatives, who offered him money in exchange for cooperation.
At their request, the agent first registered a Starlink station in his name using the details provided to him by a handler from russia.
Next, the suspect, without her knowledge, used a female acquaintance who registered another terminal in her name.
The perpetrator planned to recruit another 20 people to verify satellite communication stations for the russian army.
The SSU thwarted the enemy’s plans and apprehended the agent at a branch of one of the postal operators, where he planned to register another Starlink.
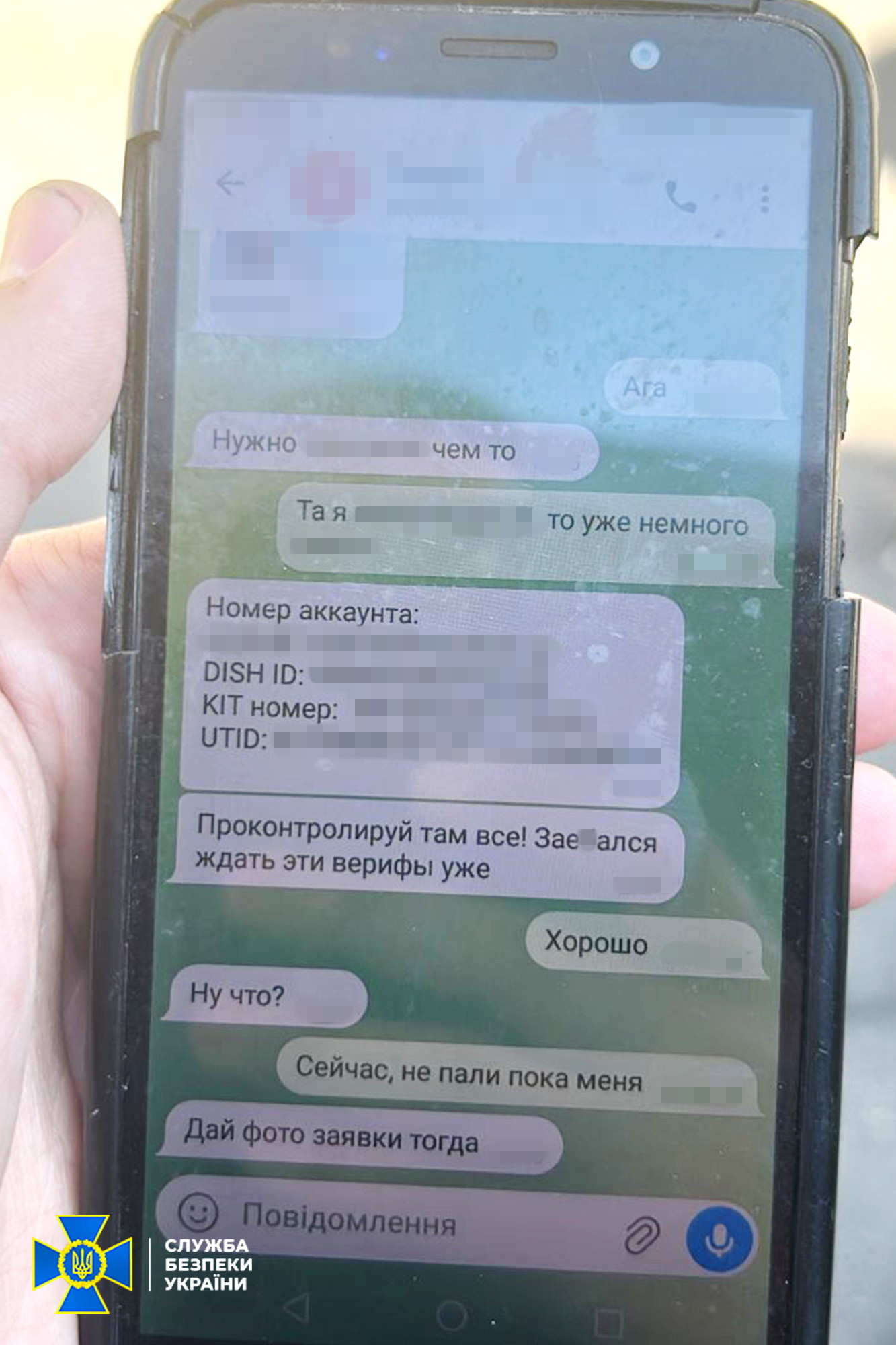
All terminals registered by the suspect have been blocked. During the searches of his home, a mobile phone containing evidence of his work for russia was found.
Security Service investigators notified the detainee of his status as a suspect under Article 111.2 of the CCU (high treason, committed under martial law).
The suspect is in custody and faces life imprisonment and confiscation of property.
The operation was carried out by the SSU Office in Kyiv and the Kyiv region under the procedural supervision of the Kyiv City Prosecutor’s Office.